NETRESEC Network Security Blog

Kubernetes Cryptojacking
In this video I take a look at a cryptojacking attack against a Kubernetes honeypot. The attackers were surprisingly quick to discover this unsecured Kubernetes deployment and use it to mine Monero for them.
The analyzed capture files can be downloaded from
https://share.netresec.com/s/S5ZG2cDKB9AbqwS?path=%2Fk3s-443
This PCAP dataset was created by Noah Spahn, Nils Hanke, Thorsten Holz, Chris Kruegel, and Giovanni Vigna as part of their research for their Container Orchestration Honeypot: Observing Attacks in the Wild paper.
The capture files named "proxy-", such as the analyzed proxy-220404-162837.pcap, were generated by PolarProxy and contain the decrypted Kubernetes API traffic to the master node. This traffic was actually TLS encrypted, but since PolarProxy was used as a TLS interception proxy we can see the Kubernetes API traffic in decrypted form.
IOC List
- attacker IP: 102.165.16.27 (PIA VPN)
- kind: DeamonSet
- name: api-proxy
- namespace: kube-system
- image: dorjik/xmrig
- mining pool: gulf.moneroocean.stream:1012
- annotation: kubectl.kubernetes.io/last-applied-configuration
- Monero wallet address: 41pdpXWNMe6NvuDASWXn6ZMdPk4N6amucCHHstNcw2y8caJNdgN4kNeW3QFfc3amCiJ9x6dh8pLboR6minjYZpgk1szkeGg
Posted by Erik Hjelmvik on Tuesday, 07 May 2024 07:50:00 (UTC/GMT)
Tags: # video # CapLoader # PolarProxy
Share:
![]()
![]()
![]()
![]() Short URL:
https://netresec.com/?b=245f018
Short URL:
https://netresec.com/?b=245f018
PolarProxy 1.0 Released
I am thrilled to announce the release of PolarProxy version 1.0 today! Several bugs that affected performance, stability and memory usage have now been resolved in our TLS inspection proxy. PolarProxy has also been updated with better logic for importing external root CA certificates and the HAProxy implementation has been improved. But the most significant addition in the 1.0 release is what we call the “TLS Firewall” mode.
TLS Firewall
PolarProxy now supports rule based logic for determining if a session should be allowed to pass through, get blocked or if the TLS encrypted data should be inspected (i.e. decrypted and re-encrypted) by the proxy. This rule based logic can be used to turn PolarProxy into a TLS firewall. As an example, the ruleset-block-malicious.json ruleset included in the new PolarProxy release blocks traffic to malicious domains in abuse.ch’s ThreatFox IOC database as well as traffic to web tracker domains listed in the EasyPrivacy filter from EasyList. This ruleset also includes an allow list in order to avoid accidentally blocking access to legitimate websites.
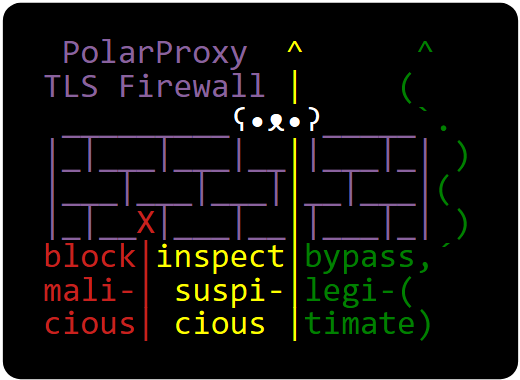
PolarProxy’s ruleset logic isn’t limited to just domain names. It is also possible to match traffic based on JA3 or JA4 hashes as well as application layer protocol information provided in the ALPN extension of a client’s TLS handshake.
For more information on the ruleset format and how to use PolarProxy as a TLS firewall, see here:
https://www.netresec.com/?page=TlsFirewall
Linux, macOS and Windows builds of the new PolarProxy release can be downloaded from here:
https://www.netresec.com/?page=PolarProxy
Posted by Erik Hjelmvik on Thursday, 02 May 2024 07:00:00 (UTC/GMT)
Tags: # PolarProxy # TLS # inspect # bypass # ThreatFox
Share:
![]()
![]()
![]()
![]() Short URL:
https://netresec.com/?b=2451e98
Short URL:
https://netresec.com/?b=2451e98
Network Forensics training at x33fcon

I will teach Network Forensics for Incident Response at the IT security conference x33fcon in Gdynia, Poland on June 11-12. In this hands-on class you will get a chance to perform network based threat hunting and deep dive into packet analysis for two days. The first day will be spent using open source tools, such as Wireshark, NetworkMiner, Suricata, Zeek, tcpflow and ngrep. On the second day we’ll also use NetworkMiner Professional and CapLoader. All training participants will get a 6 month license for CapLoader as well as NetworkMiner Professional.

Image: Motława river by Diego Delso, delso.photo (CC-BY-SA)
About x33fcon
x33fcon is held in Gdynia (Gdańsk), which is located on the Baltic coast in northern Poland. The conference’s focus is on collaboration between attackers and defenders. Their goal is to encourage security professionals to consider both perspectives while working more closely together.
More information about this two-day training can be found on Netresec’s training page.
Posted by Erik Hjelmvik on Monday, 18 March 2024 10:25:00 (UTC/GMT)
Tags: # Netresec # Training # Class # Network Forensics
Share:
![]()
![]()
![]()
![]() Short URL:
https://netresec.com/?b=2436670
Short URL:
https://netresec.com/?b=2436670
Hunting for Cobalt Strike in PCAP
In this video I analyze a pcap file with network traffic from Cobalt Strike Beacon using CapLoader.
The pcap file and Cobalt Strike malware config can be downloaded from Recorded Future's Triage sandbox.
Cobalt Strike Beacon configs can also be extracted locally with help of Didier Stevens' 1768.py or Fox-IT's dissect.cobaltstrike.
IOC List
- MD5 99516071d8f3e78e51200948bf377c4c
- SHA1 59fe505b24bdfa54ee6e4188ed8b88af9a42eb86
- SHA256 10e68f3e6c73161a1bba85ef9bada0cd79e25382ea8f8635bec4aa51bfe6c707
- JA3 a0e9f5d64349fb13191bc781f81f42e1
- JA4 t12d190800_d83cc789557e_7af1ed941c26
- IP:port 104.21.88.185:2096 (Cloudflare)
- Domain mail.googlesmail.xyz (Go Daddy)
Network Forensics Training
Are you interested in learning more about how to analyze network traffic from Cobalt Strike and other backdoors, malware and hacker tools? Then take a look at our upcoming network forensics classes!
Posted by Erik Hjelmvik on Thursday, 04 January 2024 10:12:00 (UTC/GMT)
Tags: # Cobalt Strike # CobaltStrike # Triage # JA3 # a0e9f5d64349fb13191bc781f81f42e1 # ThreatFox # CapLoader # Video # videotutorial
Share:
![]()
![]()
![]()
![]() Short URL:
https://netresec.com/?b=2410f02
Short URL:
https://netresec.com/?b=2410f02
Network Forensics Training - Spring 2024
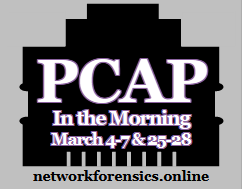
I will teach two live online network forensics classes in March, one on European morning time, and the other on US morning time. The subject for both classes is network forensics in an incident response context.
The training is split into four interactive morning sessions, so that you have the afternoon free to either practice what you learned in class or catch up with your “normal” day job. The number of attendees will be limited in order to provide a good environment for taking questions. A maximum of 15 attendees will be accepted per class. The registration will be closed once we reach this attendee limit.
-
🇪🇺 March 4-7, 2024: PCAP in the Morning Europe
⏲️ Time: 8:30 AM to 12:30 PM CET
💸 Price: € 930 EUR per student -
🇺🇸 March 25-28, 2023: PCAP in the Morning US
⏲️ Time: 9:30 AM to 1:30 PM EDT
💸 Price: $1,000 USD per student
We will be analyzing a unique 30GB PCAP data set captured during June 2020 on an Internet connected network with multiple clients, an AD server, a web server, an android tablet and some embedded devices. As you’ve probably guessed, the capture files contain traffic from multiple intrusions by various attackers, including APT style attackers and botnet operators. The initial attack vectors are using techniques like exploitation of web vulnerabilities, spear phishing, a supply chain attack and a man-on-the-side attack! In this training you'll get first-hand experience looking at C2 and backdoor protocols, such as Cobalt Strike, TrickBot, njRAT and Meterpreter.
See our training page for more info about the “PCAP in the Morning” classes.
To sign up for a class, simply send an email to sales@netresec.com with the class dates, your name and invoice address. We will then send you a PayPal payment link that you can use to complete your training registration.
Hope to see you there!

Cheers,
Erik Hjelmvik
Creator of NetworkMiner and founder of Netresec
Posted by Erik Hjelmvik on Monday, 11 December 2023 12:55:00 (UTC/GMT)
Tags: # Netresec # PCAP # Training # Network Forensics # Class
Share:
![]()
![]()
![]()
![]() Short URL:
https://netresec.com/?b=23C9979
Short URL:
https://netresec.com/?b=23C9979
CapLoader 1.9.6 Released

CapLoader now detects even more malicious protocols and includes several new features such as JA4 fingerprints, API support for sharing IOCs to ThreatFox and OSINT lookups of malware families on Malpedia. The new CapLoader 1.9.6 release also comes with several improvements of the user interface, for example interactive filtering of flows and services with regular expressions.
Detection of Malware C2 Protocols
Malware authors continually keep coming up with new C2 protocols for defenders to detect. Luckily we don’t need to manually create protocol signatures for CapLoader, we only need a few examples of traffic for a protocol to generate a statistical model that CapLoader can use to detect that protocol. We call this feature Port Independent Protocol Identification (PIPI).
We’ve added support for detecting of the following protocols in this new release of CapLoader:
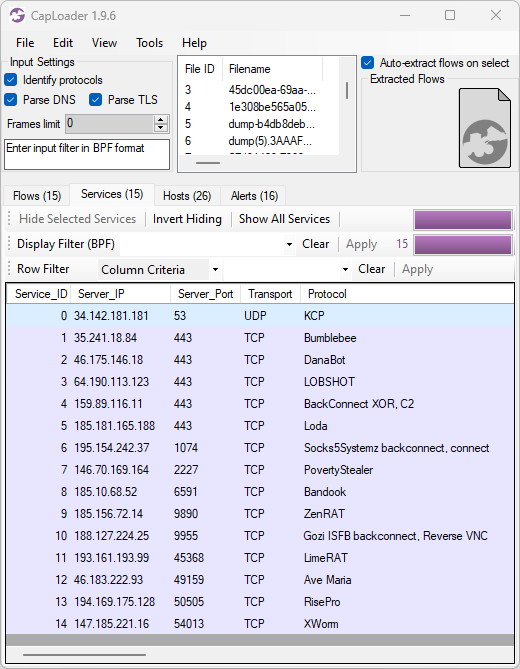
Image: Protocols identified in PCAP files with malware traffic from various sandboxes ( ANY.RUN, Hybrid-Analysis, Joe Sandbox and Triage)
Our PIPI feature can also detect protocols inside of other protocols, such as Cobalt Strike, DCRat, Emotet, Formbook, Gozi ISFB, GzipLoader and Socks5Systemz which all run on top of HTTP. It is sometimes even possible to identify malicious protocols that use TLS encryption, such as AsyncRAT, Cobalt Strike, Emotet, IcedID or Remcos. However, detection of malicious TLS encrypted protocols is a difficult challenge and might be subject to false positives.
Sharing IOCs to ThreatFox
ThreatFox is a free online service for sharing indicators of compromise (IOCs) from malware. ThreatFox can be queried for a particular malware family, such as RedLine Stealer, and it’ll return a list of URLs, domain names and IP:port pairs used for C2 communication or payload delivery for that malware. You can also query for a domain or IP address to see if it’s a known C2 address of any malware or botnet.
CapLoader has supported OSINT lookup of IP addresses and domains on ThreatFox since the release of version 1.9, but with this release we also add the ability to contribute by sharing IOCs with the infosec community. All you need to do is to enter your ThreatFox API-key in CapLoader’s settings, then right-click a flow, service or alert and select “Submit to ThreatFox”.
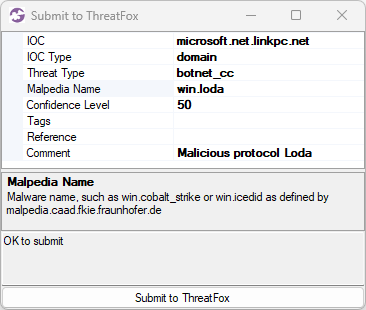
Image: Submission of microsoft.net.linkpc[.]net to ThreatFox
If the right-clicked item is an alert for a “Malicious protocol” then CapLoader will automatically populate the Mapledia Name field, as shown in the screenshot (win.loda).
TLS Client Fingerprinting with JA4
John Althouse announced the new JA4+ fingerprint methods a couple of months ago on the FoxIO blog. In short JA4+ is a suite of methods designed to fingerprint implementations of a specific set of protocols, including TLS, HTTP and SSH. As you’ve probably guessed JA4+ is a successor to the JA3 and JA3S hashes that we’ve learned to love (we added JA3 fingerprinting to NetworkMiner in 2019).
Most of the fingerprinting methods in the JA4+ suite are patent pending except for the TLS client fingerprinting method “JA4”, which FoxIO does not have patent claims and is not planning to pursue patent coverage for. We have therefore built a JA4 fingerprinting engine that we’ve included in this CapLoader release. Future releases of NetworkMiner will hopefully also include our JA4 fingerprinting engine.
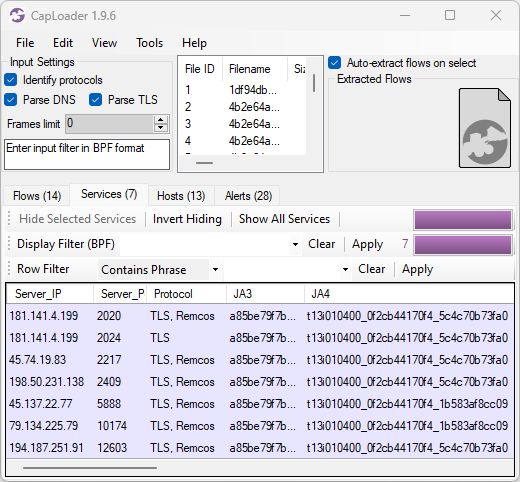
Image: JA3 and JA4 hashes of Remcos C2 traffic
JA4 is similar to JA3 in many ways, but one essential difference is that JA4 fingerprints are something of a fuzzy hash of the client’s handshake rather than a MD5 hash of the raw fingerprint. JA3’s use of MD5 hashing has received criticism, for example in academic literature, partly due to the inability to see if two JA3 hashes have similar TLS handshakes.
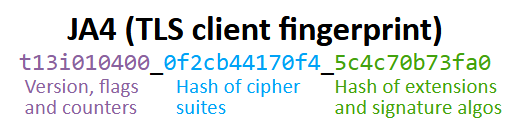
JA4 does use hashes, but instead of just being one big hash it breaks the fingerprint into three separate sections; where the first section is used in its raw (non-hashed) format and the other two sections are hashed separately. Thus, an update of a TLS implementation, which only adds one additional cipher, will increment the cipher counter in the first section of the JA4 fingerprint by one and the ciphers hash (second section) will get a new value. The hash in the last section will remain intact.
In the previous CapLoader screenshot with Remcos C2 traffic we see TLS handshakes that have the same JA3 hash (a85be79f7b569f1df5e6087b69deb493) but the JA4 fingerprints have different values (t13i010400_0f2cb44170f4_5c4c70b73fa0 and t13i010400_0f2cb44170f4_1b583af8cc09). The reason why the last JA4 section is different even though the JA3 hash is the same is because some of these TLS handshakes present a different set of signature algorithms, which is a parameter that isn't being used in JA3.
Alerts Tab
CapLoader’s Alerts tab now includes more alert types than before and each alert has a severity rating graded as follows:
- High = 4
- Medium = 3
- Low = 2
- Info = 1
A typical high-severity alert is when a known malicious protocol is detected, while an “Info” type alert can provide a heads up about traffic from things like coin mining or legitimate remote admin tools. As you can see in the screenshot below the alerts are sorted based on severity to make it easier to prioritize them.
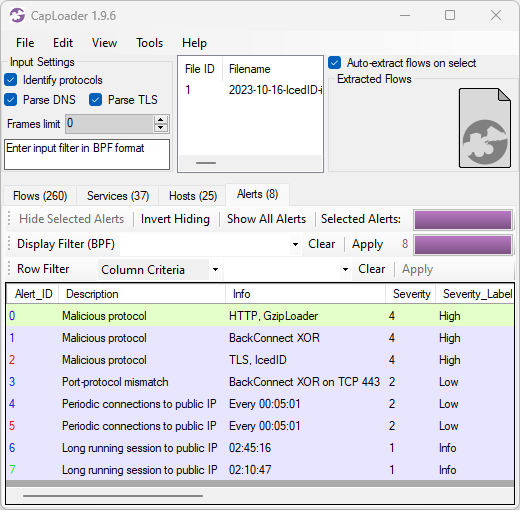
Image: CapLoader alerts for 2023-10-16-IcedID-infection.pcap
Here’s a breakdown of the alerts shown in the CapLoader screenshot above:
- GzipLoader traffic to 104.21.7.13:80 / aptekoagraliy[.]com
- BackConnect XOR traffic to 159.89.124.188:443
- IcedID over TLS traffic to 104.223.118.109:443 / seedkraproboy[.]com
- Port-protocol mismatch (non-TLS traffic to port 443) for 159.89.124.188:443
- Periodic connections every 5 minutes to 151.236.9.107:443 / lazirusairnaf[.]com
- Periodic connections every 5 minutes to 104.223.118.109:443 / seedkraproboy[.]com
- Long running TCP session to 159.89.124.188:443
- Long running TCP session to 104.248.81.48:443 / joekairbos[.]com
All these alerts are indicators of an IcedID infection, including the 5 minute C2 connection interval which I have mentioned before.
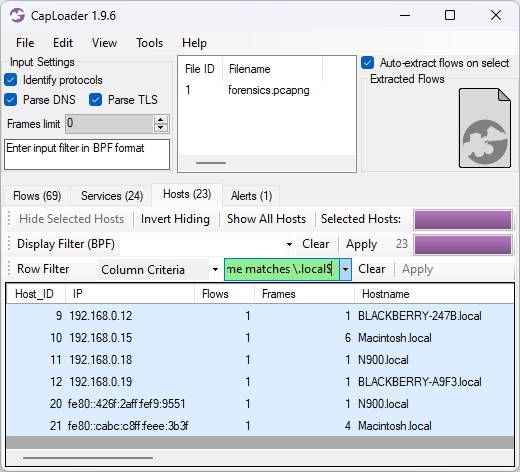
Other User Interface Improvements
CapLoader’s “Column Criteria” row filter could previously only be used to filter on columns with a specific value, such as “Protocol = TLS”. This new release of CapLoader additionally allows users to do substring matching with the “contains” keyword and regular expression (regex) matching with the “matching” keyword. In the screenshot below the Column Criteria “Hostname matches \.local$” is used to only show hosts that have a hostname ending with “.local”.
We’ve also added an often asked for feature to CapLoader, namely the ability to switch between different flows in the Transcript window.
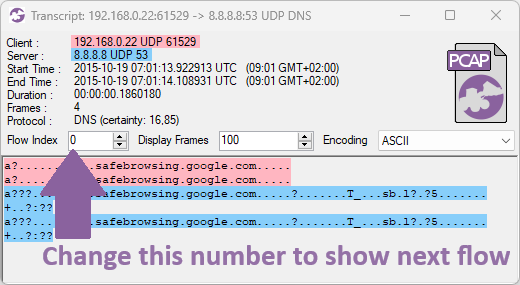
The flows you can switch between depends on how the transcript window was opened. A flow transcript opened from the Flows tab will allow switching between the flows that were visible in the list from where the transcript was opened. A transcript opened from any of the other tabs (Services, Hosts or Alerts), on the other hand, allows switching between the different flows for the particular service, host or alert that was opened.
Credits
I would like to thank Nic Cerny, Trent Healy and Fredrik Ginsberg for their input on various improvements that have been implemented in CapLoader 1.9.6.
Updating to the Latest Release
Users who have already purchased a license for CapLoader can download a free update to version 1.9.6 from our customer portal or by clicking “Check for Updates” in CapLoader’s Help menu.
Posted by Erik Hjelmvik on Wednesday, 15 November 2023 12:08:00 (UTC/GMT)
Tags: # CapLoader # ThreatFox # JA3 # IcedID # GzipLoader # regex
Share:
![]()
![]()
![]()
![]() Short URL:
https://netresec.com/?b=23B6bcd
Short URL:
https://netresec.com/?b=23B6bcd


